What IT Support Do NJ Healthcare Practices Need?
New Jersey healthcare practices face unique IT challenges. Discover the essential IT support services—from HIPAA [...]
May
LinkedIn “Social Engineering”: Protecting Your Staff from Fake Recruitment Scams
A fake recruiter message is one of the cleanest social engineering tricks around because it [...]
May
“Clean Desk” 2.0: Securing Your Home Office from Physical Data Leaks
In the traditional office, a “Clean Desk” policy was a simple habit: shred the sensitive [...]
May
The Essential Checklist for Securing Company Laptops at Home
At home, security incidents don’t look like dramatic movie hacks. They look like stepping away [...]
Apr
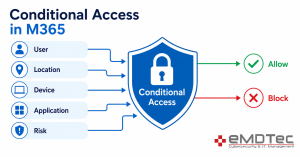
Are Consumer VPNs Safe for Work? What SMB Owners Need to Know Before Employees Connect to M365
It’s 11:47 PM on a Tuesday. Your IT provider gets a security alert: one of [...]
Apr
The 2026 Guide to Uncovering Unsanctioned Cloud Apps
If you want to uncover unsanctioned cloud apps, don’t begin with a policy. Start with [...]
Apr
Stop Ransomware in Its Tracks: A 5-Step Proactive Defense Plan
Ransomware isn’t a jump scare. It’s a slow build. In many cases, it begins days, [...]
Apr
A Small Business Roadmap for Implementing Zero-Trust Architecture
Most small businesses aren’t breached because they have no security at all. They’re breached because [...]
Apr
Zero-Trust for Small Business: No Longer Just for Tech Giants
Think about your office building. You probably have a locked front door, security staff, and [...]
Apr